North Korean Hackers Gain Access To Protocol After Posing As Most Annoying VCs At Crypto Conference
Exploit successfully executed after attackers spent six months talking about 'synergy' and asking everyone if they have time for a quick coffee.
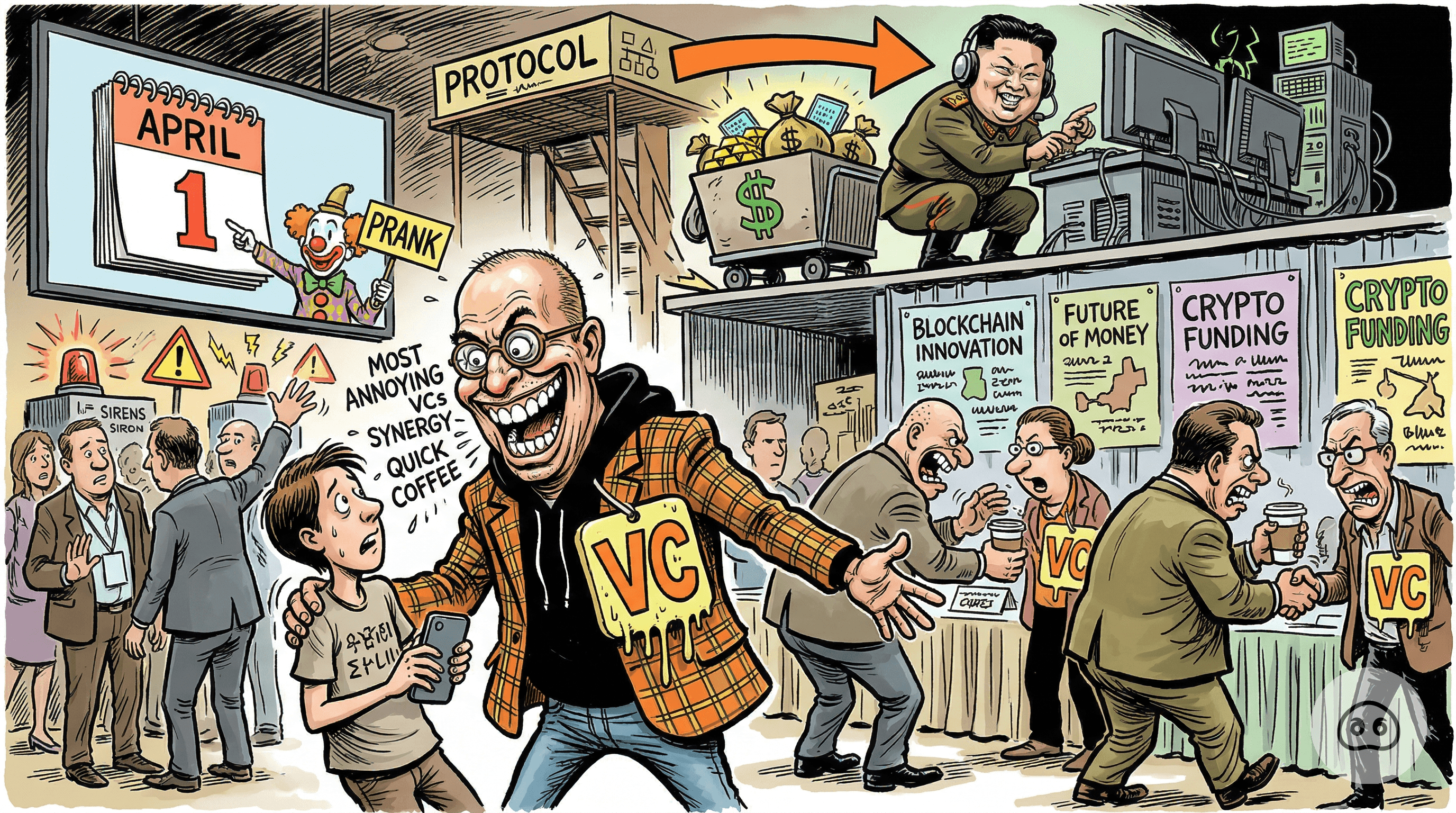
DUBAI (The Trough) — State-sponsored threat actors successfully leveraged a paradigm-shifting, zero-friction networking strategy this week—meaning they wore Patagonia vests and cornered developers at an open bar until the developers handed over their admin keys just to end the conversation.
The operatives maximized their return on investment by bootstrapping a bespoke liquidity vector with a mere $500 of seed capital. In layman's terms, they made up a digital asset out of thin air, traded it back and forth among themselves, and tricked automated pricing algorithms into valuing it at a quarter of a billion dollars.
"Their pipeline generation was flawless," said Chad Thundermetrics, Lead Synergy Architect at Drift Protocol. "They talked about 'right-sizing the decentralized ecosystem' for forty-five uninterrupted minutes. By the time they asked me to blind-sign a malicious transaction payload, I was so desperate to use the restroom I just clicked approve."
The protocol's agile, zero-second timelock framework allowed for highly optimized capital flight, streamlining the transition of $285 million in assets—including institutional-grade holdings like Fartcoin—directly to Pyongyang.
"We are a regulated financial entity, not a proactive compliance facilitator," stated Brenda Yield-Curve, VP of Frictionless Bureaucracy at Circle. "Our core competency is freezing legitimate business accounts without warning, not mitigating actual international heists."
Moving forward, the industry is plotting these new threat vectors on a scatter graph, which clearly shows that the greatest cybersecurity vulnerability in decentralized finance remains the inability to walk away from a guy saying the word 'tokenomics'.
